The following video illustrates the topic of Creating Role Mapping in Oracle Fusion HCM Security

Managing Security Using OIM
Oracle Fusion Applications are tightly integrated with Oracle Identity Management (OIM). When you hire a worker, a user account is created automatically for that worker in the OIM Lightweight Directory Access Protocol (LDAP) store. For each user:
• The user account name is generated automatically, based on the OIM configured rules for account names. By default, the user's primary work e-mail address is used.
• The user account password is generated automatically, based on the OIM configured password policy.
For some reason if a user account is not created automatically, Human Resource Specialists and Line Managers can request a user account for a worker from within Oracle Fusion HCM. You cannot assign roles to a user who has no user account. User accounts can be suspended automatically when a user has no roles.
Oracle Identity Management (OIM) maintains LDAP accounts for users of Oracle Fusion Applications. OIM also stores the definitions of job, abstract, and data roles, and holds information about roles provisioned to users. During implementation, you perform the task Run User and Roles Synchronization Process to copy any existing information about users and roles from the OIM LDAP store to the Oracle Fusion HCM product tables.
You use OIM to create implementation users and provision roles to them, manage job roles & manage role hierarchies (excluding duty roles). The task Manage Job Roles navigates automatically to OIM, where you can create and edit job roles.
Managing Security Using APM
You use Oracle Fusion Middleware Authorization Policy Manager (APM) to:
• View full role hierarchies.
• Manage the inheritance of duty-role hierarchies by job and abstract roles.
• Manage duty-role hierarchies.
• Manage and invoke data role templates.
For example, if you want to remove duty roles from a job role, you perform the task Manage Duties, which navigates to APM where you can edit the job role's duty-role inheritance.
Role Mappings
Roles provide user access to data and functions. Roles must be provisioned to users explicitly, either automatically or manually, no role is provisioned to a user by default. To provision a role to users, you define a relationship, called a Role Mapping, between the role and some conditions. You provision all types of roles using role mappings. This topic describes role mappings for automatic and manual role provisioning. Use the Manage Role Provisioning Rules or Manage HCM Role Provisioning Rules task in the Setup and Maintenance work area.
This link (video) illustrates the topic of Creating Role Mapping in Oracle Fusion HCM Security
Automatic Provisioning of Roles to Users
Role provisioning occurs automatically if
• At least one of the user's assignments matches all role-mapping conditions
• You select the Autoprovision option for the role in the role mapping.
For example, for the data role Sales Manager Finance Department, you could select the Autoprovision option and specify the following conditions.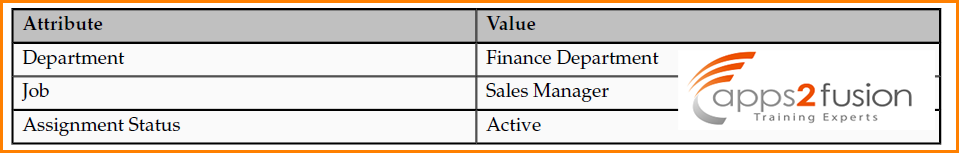
The HCM data role Sales Manager Finance Department is provisioned automatically to users with at least one assignment that satisfies all of these conditions. Automatic role provisioning occurs as soon as the user is confirmed to satisfy the role-mapping conditions, which can be when the user's assignment is either created or updated. The provisioning process also removes automatically provisioned roles from users who no longer satisfy the role-mapping conditions.
Manual Provisioning of Roles to Users
Users such as human resource (HR) specialists and line managers can provision roles manually to other users; you create a role mapping to identify roles that can be provisioned in this way. Users can provision a role to other users if:
• At least one of the assignments of the user who is provisioning the role (for example, the line manager) satisfies all conditions associated with the role mapping.
• You select the Requestable option for the role in the role mapping.
For example, for the HCM data role Quality Assurance Team Leader, you could select the Requestable option and specify the following conditions.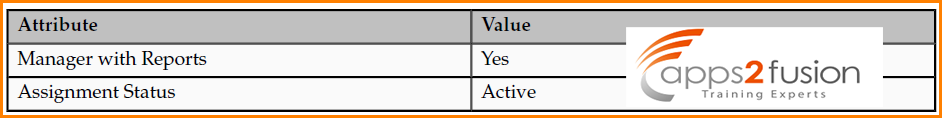
Any user with at least one assignment that satisfies both of these conditions can provision the role Quality Assurance Team Leader manually to other users, who are typically direct and indirect reports. If the user's assignment subsequently changes, there is no automatic effect on roles provisioned by this user to others; they retain manually provisioned roles until either all of their work relationships are terminated or the roles are manually deprovisioned.
Role Requests from Users
Users can request roles when reviewing their own account information; you create a role mapping to identify roles that users can request for themselves. Users can request a role if:
• At least one of their own assignments satisfies all conditions associated with the role mapping.
• You select the Self-requestable option for the role in the role mapping.
For example, for the Expenses Reporting role you could select the Self requestable option and specify the following conditions.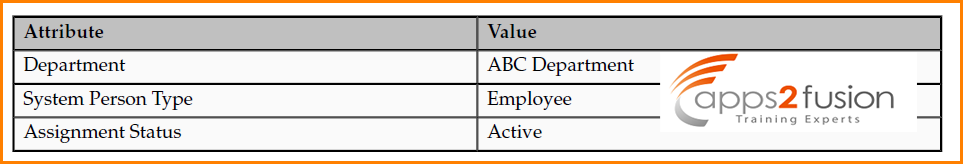
Any user with at least one assignment that satisfies all of these conditions can request the role. The user acquires the role either immediately or, if approval is required, once the request is approved. Self-requested roles are classified as manually provisioned. If the user's assignment subsequently changes, there is no automatic effect on self-requested roles. Users retain manually provisioned roles until either all of their work relationships are terminated or the roles are manually deprovisioned.
Immediate Provisioning of Roles
When you create a role mapping, you can apply autoprovisioning from the role mapping itself. In this case, all assignments and role mappings in the enterprise are reviewed. Roles are:
• Provisioned immediately to all users who do not currently have roles for which they are eligible
• Deprovisioned immediately from users who are no longer eligible for roles that they currently have
Immediate autoprovisioning from the role mapping enables bulk automatic provisioning of roles to a group of users who are identified by the role-mapping conditions. For example, if you create a new department after a merger, you can provision relevant roles to all users in the new department by applying
Autoprovisioning immediately. To provision roles immediately to a single user, the user's line manager or HR specialists can autoprovision roles from that user's account.
Role Deprovisioning
Users lose automatically provisioned roles when they no longer satisfy the role-mapping conditions. For example, a line manager loses an automatically provisioned line manager role when he or she stops being a line manager. You can also manually deprovision automatically provisioned roles at any time.
Users lose manually provisioned roles automatically only when all of their work relationships are terminated. Otherwise, users keep manually provisioned roles until you deprovision them manually.
Roles at Termination
When you terminate a work relationship, the user automatically loses all automatically provisioned roles for which he or she no longer qualifies. The user loses manually provisioned roles only if he or she has no other work relationships. Otherwise, the user keeps manually provisioned roles until you remove them manually. The user who's terminating a work relationship specifies when the user loses roles. Deprovisioning can occur as soon as the termination is submitted or approved and on the day after the termination date.
Role mappings can provision roles to users automatically at termination. For example, a terminated worker could acquire the custom role Retiree at termination based on assignment status and person type values.
Reversing a termination reinstates any roles that the user lost automatically at termination and removes any that the user acquired automatically at termination.
Date-Effective Changes to Assignments
Automatic role provisioning and deprovisioning are based on current data. For a future-dated transaction, such as a future promotion, role provisioning occurs on the day the changes take effect. The Send Pending LDAP Requests process identifies future-dated transactions and manages role provisioning and deprovisioning at the appropriate time. These role-provisioning changes take effect on the system date. Therefore, a delay of up to 24 hours may occur before users in other time zones acquire their roles.
Role-Mapping Names
The names of role mappings must be unique in the enterprise. You are recommended to devise a naming scheme that reveals the scope of each role mapping. For example: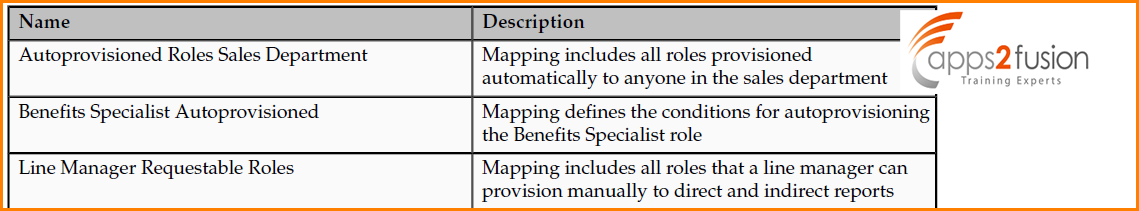
My next article covers the topic of Creating HCM Data Roles in Oracle Fusion HCM Security



Comments
now and finally got the bravery to go ahead and give you a shout out from New Caney Texas!
Just wanted to mention keep up the great job!
Feel free to visit my page :: body sculpting spa: https://imle.gen.tv.tr/Siteler/how-electrical-stimulation-is-utilized-in-physical-therapy/
A design like yours with a few simple adjustements would really
make my blog jump out. Please let me know where you got your design. Thank you
It's simple, yet effective. A lot of times it's very hard to get that
"perfect balance" between usability and visual appearance.
I must say that you've done a awesome job with this.
Additionally, the blog loads extremely quick for me on Opera.
Exceptional Blog!
a quick visit this web site and be up to date everyday.
RSS feed for comments to this post