This Oracle HCM Security Training will teach you about the Fusion HCM role-based security model. Our expert instructors will help you gain hands-on experience with the UIs used to manage security in Fusion HCM. This course is relevant for any customers using Fusion Applications through Release 11.1.7 This course is appropriate for both Oracle Cloud and on-premises deployments. By taking this course, you'll learn how to plan and implement security in Fusion HCM. Our expert instructors will help you explore how HCM security works with Oracle's BI Reporting tools. You'll also learn some advanced tips for implementing security, using features like Areas of Responsibility to minimize the number of data roles you need to create.
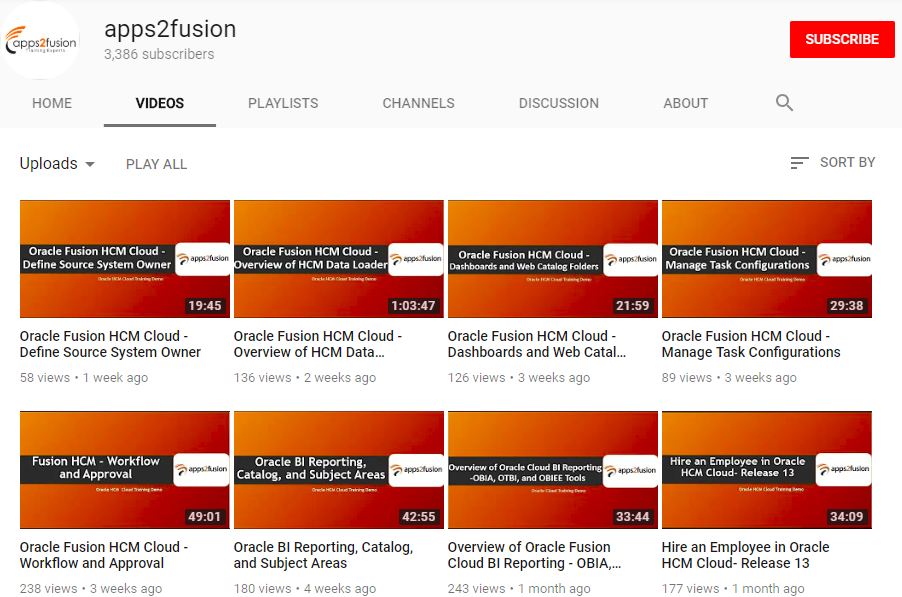
Preview
By the end of this training you will Learn To:
- Identify and manage the different types of roles, including data, abstract, job, and duty roles
- Create role-provisioning rules
- Create security profiles to restrict data access.
- Create data roles and assign security profiles to them.
- Create implementation users.
- Provision roles to users.
- Create a custom job role using Oracle Identify Manager (OIM).
- Create a custom duty role using Authorization Policy Manager (APM).
Course Contents
Day 1
Security Overview
Role-Based Security Model
Predefined HCM Roles
Role Inheritance
Role Types
Security Privileges
Customizing Security for Your Needs
Security Profiles and Data Roles
Data Security Through Security Profiles
HCM Security Profile Types
Predefined HCM Security Profiles
HCM Security Profiles Best Practices
Key Points for Creating Security Profiles
Creating Security Profiles and Assigning to a New Data Role
Assigning Security Profiles to Existing Roles
Editing Security Profiles
Day 2
User and Role Provisioning
User Account Creation and Maintenance Scenarios
User Account Provisioning
Enterprise-Level User and Role-Provisioning Options
Provisioning Roles to Users: Overview
Defining Role-Provisioning Rules
Integration with New Hire Flow
Implementation Users
Creating a New User and Assigning a Data Role
HCM Security Management Data Stores
User Interface Overview
HCM Security Management Data Stores
Setup Tools and Tasks
Access to Security Tasks
Managing Job Roles and Abstract Roles
Regenerating Data Roles
Creating a New Job Role
Creating a New Data Role and Assigning to User
Using Security Console
User Management / General Administration